In today’s digital-first world, the ability to confirm someone’s identity online is critical to protecting businesses and their customers. As a result, authentication and verification have become foundational components of digital identity processes. But while these terms are often used interchangeably, there’s a distinct difference between verification and authentication—and understanding it is key to building secure, user-friendly systems.
This article breaks down the difference between verification and authentication, explains how each fits into the digital identity lifecycle, and explores current trends shaping how businesses verify and authenticate users. Whether you’re evaluating your fraud prevention strategy or implementing new identity tools, it’s essential to understand how authentication and verification work together to build trust and prevent abuse.
Table of Contents
What is digital identification?
Digital identification is the process of establishing who someone claims to be based on the information they provide. It forms the foundation for both identity verification and authentication.
When a user signs up for a new service, they’re typically asked to submit identifying details such as their name, phone number, email address, date of birth, or physical address. These attributes—along with metadata like device type, IP address, and browser—make up a person’s “digital identity.”
The level of information required varies depending on the service. For example, opening a bank account requires stricter checks than creating a profile on a social media platform.
At its core, digital identity is a collection of data points that can be linked to a specific individual or account. Once collected, these details must be verified to confirm that they are accurate and belong to a real person. From there, authentication ensures that the same person can securely access the account in the future.
What is verification?
Verification is the process of confirming the identity of a user, device, or entity before granting access to a system or service. It typically happens at the beginning of a digital interaction—such as during account creation, a password reset, or when logging in from a new device.
At its core, identity verification ensures that someone is who they claim to be. This process involves checking submitted information—like a phone number, date of birth, email address, or even a government-issued ID—against trusted data sources to confirm its validity. For example, a business might send a one-time SMS code to verify that a phone number truly belongs to the person attempting to register.
The scope of auth verification varies by industry and use case. In high-risk scenarios like opening a financial account, verification may involve document scanning, biometric matching, or database checks. In lower-risk environments, it could be as simple as confirming an email address.
Ultimately, authentic verification is subjective—an individual is considered “verified” only once the organization is confident in the legitimacy of their identity. The goal is to reduce fraud and build a foundation of trust before moving on to authentication.
What is authentication?
Authentication is the process of proving a verified identity by using credentials like passwords, one-time passcodes (OTPs), or biometric data. It takes place after verification, ensuring that the person trying to access an account is the rightful owner of the previously verified identity.
A common example of authentication is entering a password and an SMS OTP to log into your online banking account.
Authentication is a repeated process—it happens every time a user attempts to access a protected system. It’s often so seamless that users don’t consciously think of it as an authentication check—just as the normal way they log in.
To authenticate, users must present one or more factors from three core categories:
- Something you know: A knowledge-based factor like a password, PIN, or a security question.
- Something you have: A possession-based factor such as an OTP, a hardware token, or a mobile authentication app.
- Something you are: A biometric factor like a fingerprint or facial recognition. This is increasingly used in biometric authentication vs verification scenarios for high-security access.
Authentication can be either single-factor (using just one method) or multifactor (requiring two or more), depending on the security level required. Multifactor authentication (MFA) adds stronger protection against fraud and unauthorized access.
Here’s a simplified breakdown of the digital identity process:
- Digital identity: A person claims to be someone by providing identifying information.
- Verification: The business confirms that the identity is real and valid.
- Authentication: Each time the person logs in, they authenticate using one or more methods to confirm their right to access the account.
Understanding the difference between authentication and verification—and how they work together—is essential for any secure digital interaction. Where verification answers “Are you who you say you are?,” authentication answers “Are you still the same person coming back in?”
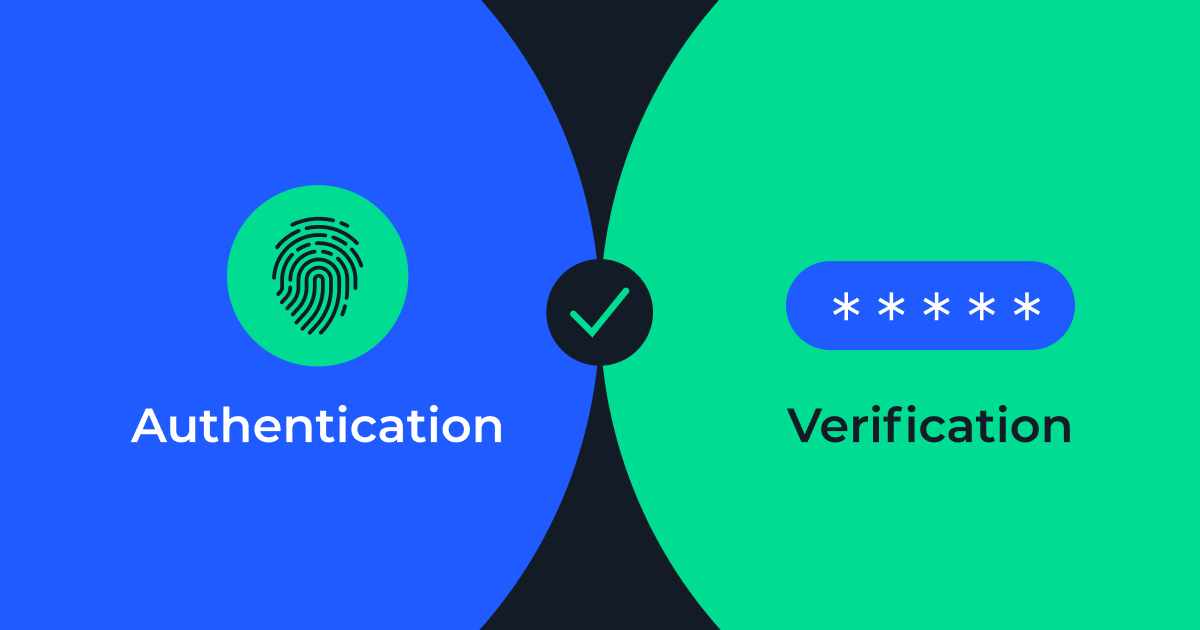
What is the difference between authentication and verification?
While closely related, verification and authentication serve different purposes in the digital identity lifecycle.
- Verification confirms that the identity a person provides is valid and trustworthy.
- Authentication ensures that the person attempting to access an account is the same individual who was previously verified.
Put simply: Verification answers “Who are you?” while authentication asks, “Are you really the same person coming back?”
Understanding the authentication vs verification meaning is essential when building secure and user-friendly identity flows. It’s not just about thwarting fraud—it’s also about meeting compliance standards and maintaining a seamless customer experience.
There’s no single rulebook for when or how to verify vs authenticate a user. The right approach depends on several key factors:
- Regulatory requirements in your industry or region.
- Risk profile of your product or service.
- Sensitivity of the data or transaction involved.
- Level of assurance needed based on the use case.
For example, financial institutions typically need to meet strict Know Your Customer (KYC) and Anti-Money Laundering (AML) requirements, which demand more thorough identity verification. In contrast, lower-risk platforms—like entertainment or e-commerce services—may rely on simpler methods, such as email verification or a basic password login.
Whether you’re managing low-risk interactions or high-value transactions, aligning your identity verification and authentication practices with your business needs and user expectations is key to reducing fraud, improving trust, and delivering a secure digital experience. And understanding the difference between validation vs authentication—alongside the nuances of authenticate vs validate and authenticate vs verify—is foundational to making the right choices.
Verification vs authentication: A quick comparison table
| Feature | Verification | Authentication |
| Purpose | Confirms identity exists | Proves identity matches credentials |
| When it happens | Before authentication | During or after verification |
| Example | SMS verification code for sign-up | 2FA login using SMS OTP |
| Security level | Basic | Stronger, depends on the method |
| Common methods | Email, SMS, phone verification | Passwords, biometrics, MFA |
Key use cases of identity verification vs authentication
Understanding when to validate vs authenticate is essential for building secure, compliant, and user-friendly digital experiences. While verification and authentication are closely related, each plays a unique role in managing identity and access—and knowing when to apply them can make all the difference in protecting your users and your platform.
When to use verification
Verification takes place at the beginning of a relationship, helping businesses confirm the legitimacy of a user’s identity. This authenticity verification ensures that the person claiming an identity can be validated against trusted data sources.
Key scenarios where verification is essential include:
- New user onboarding: Validating a phone number or email ensures a user can be contacted and helps prevent fake or duplicate account creation.
- Fraud prevention: Verification processes like phone intelligence APIs and CAPTCHA help detect and stop bot registrations and malicious signups.
- KYC compliance: Financial services and other regulated industries must verify identities using government-issued IDs or authoritative data sources to meet legal requirements.
These actions speak directly to the difference between verification and authentication—verification is the first step in establishing trust. It’s also where concepts like identity validation vs verification and identify vs verify come into play, especially when layered with regulations and industry standards.
When to use authentication
Authentication follows verification, checking whether the person accessing an account is the same one who was previously verified. This is the core of identity authentication and verification, and it’s used continuously throughout a user’s journey.
Key moments that require authentication include:
- Logging into a platform: A password, fingerprint scan, or facial recognition check helps confirm rightful access.
- Completing a high-risk transaction: Financial actions or changes to sensitive settings require extra assurance that the user is legitimate.
- Implementing MFA: Using a combination of factors—like an SMS OTP plus a biometric scan—strengthens authentication and validation mechanisms.
These use cases demonstrate the difference between authentication and validation and reinforce how important it is to align authentication methods with risk. Whether you’re focused on auth verify procedures, auth verified meaning, or distinguishing between authentication vs validation, knowing when to apply authentication is a cornerstone of strong identity security.
Both verification and authentication must be carefully designed into the user experience. Understanding the difference between validation, verification, and authentication is key to preventing fraud, meeting compliance needs, and safeguarding user trust.
Identity verification examples
- Phone number verification for account sign-ups
Example: A social media platform wants to prevent fake accounts and bot registrations.
Telesign’s solution:
- When a user signs up, the platform sends an SMS verification code via Telesign’s Verify API.
- The user must enter the OTP to confirm they own the phone number.
- If successful, the platform proceeds with account creation.
Benefit: Protects against fraud, reduces fake sign-ups, and ensures real user identities.
- Combating fraud in e-Commerce transactions
Example: An e-Commerce site needs to validate customers before processing high-value orders.
Telesign’s solution:
- The retailer uses Telesign’s Phone ID API to check if the phone number is valid, active, and matches customer details.
- If the number is flagged as risky (e.g., recently recycled, virtual, or fraudulent), the order is blocked or requires extra verification.
Benefit: Reduces chargebacks, mitigates fraudulent transactions, and enhances customer trust.
- Identity verification for FinTech and Banking
Example: A digital banking app must comply with Know Your Customer (KYC) regulations before opening accounts.
Telesign’s solution:
- The bank uses Telesign’s Verify API to validate that the provided phone number belongs to the actual user.
- Telesign’s Phone Intelligence API helps detect high-risk numbers, such as burner phones or recently deactivated numbers.
- If flagged, additional verification steps (e.g., government ID check) are required.
Benefit: Reduces identity fraud, ensures compliance with financial regulations, and protects against unauthorized account creation.
Authentication examples
- Two-factor authentication (2FA) for secure logins
Example: A SaaS platform wants to enhance login security by requiring an additional step beyond just a password.
Telesign’s solution:
- After a user enters their username and password, Telesign sends an SMS OTP to their registered phone number.
- The user must enter this one-time code to complete login authentication.
- If the code matches, access is granted.
Benefit: Strengthens account security, prevents credential stuffing, and reduces the risk of stolen passwords.
- Adaptive authentication for suspicious login attempts
Example: A banking app detects an unusual login attempt from a new device and needs to verify identity before granting access.
Telesign’s solution:
- Risk-based authentication (RBA): The bank analyzes login patterns and device risk (via Telesign’s Intelligence API).
- If the attempt seems risky (e.g., new location or device), the system triggers an extra SMS authentication step.
- The user must enter an OTP to confirm the login is legitimate.
Benefit: Prevents account takeovers, balances security with user experience, and reduces friction for trusted users.
- Authentication for password resets and account recovery
Example: A user forgets their password and needs to reset it securely.
Telesign’s solution:
- Instead of sending a reset link via email (which is vulnerable to phishing), the system sends an SMS OTP to the registered phone number.
- The user enters the OTP to verify their identity before setting a new password.
Benefit: Prevents unauthorized password resets, ensures only the account owner can regain access, and reduces support costs for businesses.
Risks and implications of weak verification and authentication
Implementing robust verification and authentication processes isn’t just a best practice—it’s a critical defense against a wide range of digital threats. Failing to properly verify or authenticate users leaves your business vulnerable to fraud, reputational damage, and regulatory penalties. Here’s what’s at stake—and how to strengthen your defenses.
Risks of weak verification
When identity verification is too basic—or missing altogether—fraudsters can slip through the cracks. Weak verification practices open the door to:
- Fake account creation: Fraudsters use synthetic or stolen identities to create accounts for illegal activities.
- Bot registrations: Automated bots can mass-register accounts, skew platform metrics, and prepare for future abuse.
- First-party and third-party fraud: Without validating that a user is real, businesses risk onboarding bad actors with malicious intent.
These risks often stem from relying solely on low-effort checks, such as email validation, without deeper analysis of the user’s identity or device.
Risks of weak authentication
Even after a user is verified, weak authentication protocols leave accounts exposed to unauthorized access. Common threats include:
- Account takeovers (ATO): Attackers use stolen credentials or brute-force tactics to gain control of legitimate user accounts.
- Password leaks: Reused or weak passwords are prime targets in data breaches and credential-stuffing attacks.
- SIM swap attacks: Fraudsters hijack phone numbers to intercept OTPs and bypass SMS-based authentication.
Authentication must evolve beyond simple passwords and basic OTPs to defend against these growing threats.
How to strengthen both verification and authentication
To reduce fraud and maintain trust, businesses need to adopt smarter, layered approaches:
- Phone intelligence APIs: Tools that analyze phone number metadata—such as whether a number is active, recycled, or high-risk—can prevent fake account creation and improve identity verification accuracy.
- Risk-based authentication: Adaptive systems analyze behavior patterns, geolocation, device reputation, and other contextual data to dynamically adjust authentication requirements. This balances security with user experience.
- Passwordless authentication: Technologies like biometrics (fingerprints, face scans) and WebAuthn offer secure, frictionless alternatives to traditional login methods—reducing reliance on vulnerable passwords.
Strengthening your auth verification strategy through intelligent tools and modern frameworks is key to stopping fraud before it starts—and ensuring that only the right people gain access to your platform.
Technical insights into verification and authentication
As digital identity threats grow more sophisticated, so do the technologies that help prevent them. From the layered approach of authentication factors to cutting-edge APIs and AI-powered systems, there’s a lot happening behind the scenes to ensure that users are truly who they say they are.
Authentication factors explained
Strong authentication relies on one or more of the following factors to validate a user’s identity:
- Something you know: This includes passwords, PINs, and security questions. While common, these are vulnerable to phishing, leaks, and brute-force attacks.
- Something you have: A physical object like a mobile phone, smart card, or hardware token. This is often used in two-factor authentication (2FA), such as receiving an OTP via SMS.
- Something you are: Biometric identifiers such as a fingerprint, facial recognition, or voice. These are harder to steal or replicate and support modern, passwordless authentication methods.
The more factors used—especially across categories—the stronger the authentication. This is the principle behind MFA.
How AI and Machine Learning enhance verification and authentication
Artificial intelligence (AI) and machine learning (ML) are transforming the way we handle both identity authentication and verification.
AI-driven systems can analyze vast amounts of data in real time to detect anomalies, predict fraudulent behavior, and personalize the authentication experience. For example:
- Behavioral analysis: AI can flag login attempts that don’t match normal user patterns, such as device changes or unexpected geolocations.
- Document verification: ML models can assess ID documents for tampering, mismatches, or forgery during the verification process.
- Continuous authentication: Some systems use behavioral biometrics—like typing rhythm or touchscreen gestures—to silently re-authenticate users throughout a session
By learning and adapting over time, AI-based tools reduce friction for legitimate users while keeping fraudsters out.
APIs for automated verification and authentication
APIs enable businesses to integrate auth verification directly into their systems without building infrastructure from scratch. For example:
- Phone verification APIs, like Telesign’s Phone ID API, can confirm if a phone number is real, active, and associated with a particular user. This helps prevent fake account signups and supports identity verification during onboarding.
- Authentication APIs can facilitate one-time passcodes, push-based authentication, or even biometric login flows—streamlining the process while maintaining security.
With the right APIs in place, companies can automate key checkpoints in the identity verification and authentication journey, enhancing both efficiency and accuracy.
Real-world impact of verification and authentication
Strong verification and authentication are no longer optional—they’re standard practice across industries where trust and security are critical.
For example, banks commonly implement SMS verification at account registration and follow up with MFA when users log in or initiate high-risk actions. This layered defense helps prevent fraud and account takeovers by confirming both the user’s identity and ongoing access legitimacy.
The risks of not securing authentication are clear. According to the IBM 2024 Cost of a Data Breach Report, stolen or compromised credentials were the most common cause of breaches and one of the costliest, averaging $4.78 million per incident. Additionally, ENISA (the EU Agency for Cybersecurity) highlights poor authentication as a key factor in phishing-related attacks, which continue to rise across both public and private sectors.
These insights emphasize the urgent need for businesses to strengthen both verification and authentication to mitigate risk and preserve trust.
Telesign’s role in securing user accounts
Use case 1: Enhancing account security in entertainment platforms
Customer: Ubisoft
Industry: Gaming
Challenge: With over 141 million unique players across consoles and PC, Ubisoft faced challenges related to account takeovers, fraudulent transactions, and the creation of fake accounts—issues that threatened the integrity of the gaming experience.
Solution: Ubisoft partnered with Telesign to integrate mobile phone number verification into their account security strategy. This approach demonstrates the practical difference between verification and authentication in action.
- Phone number verification: During account creation, users are prompted to verify their mobile number via SMS one-time passcode. This step confirms the number is real, active, and owned by the user—supporting strong authenticity verification and reducing the likelihood of fake account creation.
- Enhanced account integrity: By validating phone numbers early, Ubisoft filters out bots and bad actors, securing legitimate player access before later authentication events such as logins or in-game purchases.
Results:
- Reduced fake accounts: By verifying phone numbers at the point of registration, Ubisoft effectively blocked bots and bad actors, helping ensure that only legitimate users gained access.
- Improved player trust and platform safety: With fewer fraudulent accounts and reduced risk of takeovers, players enjoyed a more secure and trustworthy gaming environment.
- Smarter onboarding: The streamlined verification process supported faster, more efficient user onboarding without compromising security.
Why It matters: This use case shows how verification is used to confirm a user’s identity before any login activity takes place—clearly illustrating the verify vs authenticate process. With strong verification up front, authentication later becomes more reliable. It’s a practical example of how investing in auth verification creates a safer, more scalable user experience.
Use case 2: Building trusted customer experiences in online marketplaces
Customer: Fiverr
Industry: Online Marketplace
Challenge: As a global platform connecting businesses with freelancers across over 400 categories, Fiverr needed to ensure the authenticity of its users to maintain trust and security. Initially, Fiverr relied on email for user verification, but as the platform grew, it became evident that email alone was insufficient for robust identity authentication and verification. Weak passwords and the potential for email compromise posed significant risks, highlighting the need for a more secure method to verify user identities.
Solution: Fiverr partnered with Telesign to implement a comprehensive verification and authentication strategy:
- Phone number verification: During account registration, users are prompted to verify their phone numbers by entering an OTP sent via SMS or voice call. This process ensures that each account is linked to a valid phone number, enhancing authenticity verification and reducing the likelihood of fake accounts.
- Two-factor authentication (2FA): For sensitive actions, such as changing personal or financial information, Fiverr employs 2FA. Users must provide an additional verification code sent to their registered phone number, adding an extra layer of security and exemplifying the difference between verification and authentication.
- Risk-based decisions: By utilizing risk recommendations, Telesign helped Fiverr to understand the risk associated with new user registrations by analyzing various factors, including phone number type, telecom carrier, and geographic location. High-risk accounts are flagged or blocked, demonstrating the importance of identity validation vs verification in maintaining platform integrity.
Results:
- 60% reduction in unauthorized withdrawals: The implementation of these security measures led to a significant decrease in unauthorized account activities, showcasing the effectiveness of robust auth verification processes.
- Enhanced user trust: By prioritizing security through comprehensive identity authentication and verification, Fiverr strengthened user confidence in the platform, fostering a safer and more reliable marketplace environment.
Why it matters: This use case illustrates the critical role of integrating verification and authentication mechanisms in online marketplaces. By implementing phone number verification and 2FA, Fiverr effectively addressed the difference between verification and authentication, ensuring that users are both genuine during registration and authorized during sensitive transactions. This approach not only mitigates fraud but also enhances user trust and platform credibility.
Use case 3: Streamlining onboarding and verification in financial institutions
Customer: Amount
Industry: Financial Technology
Challenge: As financial institutions rapidly transitioned to digital platforms, Amount faced the challenge of delivering seamless customer onboarding while keeping fraud in check. Meeting KYC requirements in a fully digital environment demanded a reliable way to verify users without increasing friction or manual intervention.
Solution: Amount partnered with Telesign to enhance its onboarding process using robust verification tools.
- SMS and voice verification: During sign-up, users receive an OTP) via SMS or voice call to verify their phone number. This step ensures that the number is real and tied to a legitimate user—supporting authenticity verification before account access.
- Self-service identity confirmation: This approach allowed users to complete the onboarding process without human review, improving speed and efficiency while maintaining strong identity verification controls.
Results:
- Increased conversion rates: The streamlined flow led to higher account creation rates without sacrificing identity authentication and verification standards.
- 85% self-verification success: A significant majority of users were able to complete the auth verification process via self-service methods, reducing manual workload and operational costs.
- Reduced fraud risk: By confirming the user’s identity through phone number verification, Amount was able to minimize exposure to fraudulent activity at the account creation stage.
Why it matters: This example illustrates the difference between verification and authentication in real-world terms. Amount uses phone-based verification to establish identity before granting access—where authentication comes into play later when a verified user logs in or transacts. It also underscores how important it is to align identity validation vs verification strategies to meet regulatory needs while supporting smooth digital journeys.
Build smarter identity flows with verified trust
As digital ecosystems expand, the need for strong, coordinated identity protection has never been more urgent. Understanding the difference between verification and authentication—and knowing when and how to apply each—is essential to building secure, seamless, and trustworthy digital experiences.
Verification confirms that a user’s identity is legitimate. Authentication ensures that the person attempting to access an account is the same one who was previously verified. Together, they form the foundation of every secure interaction in your platform.
Telesign helps businesses strengthen both steps of this journey. With intelligent phone verification APIs and adaptive SMS authentication solutions, Telesign empowers you to confirm identities at sign-up, detect recycled or suspicious phone numbers, and authenticate returning users without adding unnecessary friction. Our technology is powered by global carrier data, machine learning models, and real-time risk insights—making it easier to detect fake accounts, prevent fraud, and maintain trust at scale.
Mitigating identity-related risks requires a layered approach. Companies should combine device and phone intelligence with adaptive, risk-based authentication that can respond to unusual behavior, login patterns, or suspicious location data. By moving toward passwordless authentication using biometrics or secure device-based credentials, businesses can reduce their reliance on outdated login methods and improve both security and user experience.
For consumers, the growing use of recycled phone numbers means you should be cautious when changing numbers or using OTPs to access critical accounts. For businesses, integrating number intelligence can prevent sending verification messages to unintended users—protecting both your brand and your customers.
The bottom line: verification and authentication are more than just compliance checkpoints—they’re powerful tools for reducing fraud, increasing conversions, and fostering digital trust. Telesign delivers the advanced verification and authentication solutions that modern businesses need to stay ahead of evolving threats and user expectations.
Talk to our experts today to learn how Telesign can help you secure every interaction—starting from the very first.
FAQ: Verification vs authentication
Verification is used to confirm that a person’s claimed identity is real and trustworthy—typically during onboarding or registration. Authentication, on the other hand, is used to confirm that the same person is accessing their account in future interactions. In short, verification validates identity, while authentication protects access.
No. Authentication depends on prior verification. You can’t authenticate someone unless you’ve already verified who they are. Verification lays the foundation by confirming a person’s identity—authentication builds on that by ensuring the right person returns to use that identity securely.
Secure authentication should follow a layered approach using:
Multifactor authentication with at least two of the following: something you know, something you have, something you are
Risk-based authentication that adapts based on user behavior or device data
Passwordless methods such as biometrics or hardware-based credentials
Monitoring tools to detect anomalies or suspicious access attempts
Combining these practices reduces the risk of ATOs phishing, and other security threats.
Biometric login—like using a fingerprint or facial recognition—is a type of authentication check. It confirms that the person attempting to access an account is the same verified individual. While biometrics can support identity verification in some scenarios (e.g., at signup with a government ID), in most digital use cases, they are used to authenticate a returning user.