Building a successful online or mobile application company may bring an unfortunate side effect: the more popular a company becomes, the more it becomes a target. And while fraud has always posed a challenge in business, it’s the methods that constantly evolve. One of the most significant current threats to companies operating online comes in the form of malicious, relentless, and elusive fake users. These individuals sneak their way into online communities by creating fake accounts, wreaking havoc among legitimate users, and making a living out of tarnishing brand reputations.
It can be hard to accurately and efficiently detect fraudulent new account sign-ups, especially when fraudsters continuously evolve their attack mechanisms. Fake accounts open the door to financial losses for your business while impacting your user abandonment rates, customer lifetime value, and net-promoter scores.
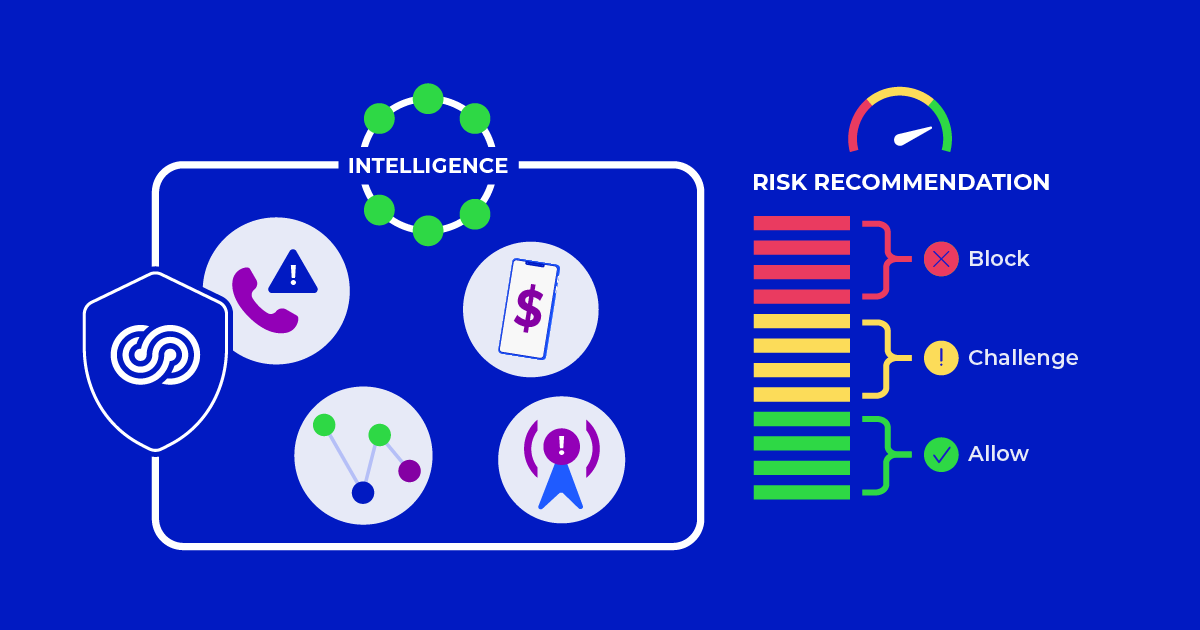
That’s why we built Telesign Intelligence: a product that can detect suspicious behavior from users’ phone numbers in milliseconds. By embedding Intelligence into your new account workflow, our recommendations can help you spot and stop potential fraudsters from entering your digital ecosystem.
Table of Contents
How Intelligence detects fake new accounts
Intelligence evaluates a phone number using billions of static and behavioral attributes to help you evaluate the risk in your interactions. It calculates a risk recommendation for each phone number, which is complemented by a set of insights and reason codes to facilitate a comprehensive understanding of the phone number’s risk profile.
Some data points that can indicate the presence of fake accounts include:
- Abnormal phone number activity: An unusually large volume of traffic and activity from a phone number within a short time may indicate risky interactions.
- Bot-like behavior: Sending far more SMS messages than would be typical of, or even possible, for a human, is one example of bot-like behavior.
Detect bots, fake accounts, and spammers at scale
Intelligence detects phone numbers with fraudulent attributes, bulk account creation, and the exploitation of sign-up promotions. With global coverage and split-second decision making, Intelligence arms you with the information you need to keep out potential fraudsters while safeguarding your bottom line.
Improve your fraud detection without introducing friction
Friction, such as too many customer inputs, verification challenges, or country blocking, can increase new user abandonment rates. Intelligence detects fraud without overhauling your user verification infrastructure. Just layer in data from Intelligence in front of your existing new account verification workflow to gain extra security without materially impacting the conversion rates of legitimate new sign-ups.
Seamlessly connect with your existing CPaaS vendor
You don’t have to switch verification vendors to improve your security with Intelligence. Intelligence works alongside all messaging and CPaaS vendors so you and your team can focus on increasing your sign-ups instead of rebuilding your verification infrastructure.
Try Intelligence with a free trial
You can try Intelligence through a free trial account. You’ll get instant access to an API Key and complimentary test credits to run risk assessments on test phone numbers.
Make sure to visit the Telesign Developer Center to learn more about how development teams can build and optimize their messaging and verification workflows with our APIs.